Episodes

Sunday Jun 20, 2010
Modern Replacement for HijackThis
Sunday Jun 20, 2010
Sunday Jun 20, 2010
OTL by OldTimer – A Modern Replacement for HijackThis
OTL by OldTimer is like HijackThis — on steroids. OTL scans your system for malware, and produces detailed logs. It’s primarily a malware diagnostic tool, but has advanced removal abilities. It is used alone, or with other tools to remove malware completely.OTL is a flexible, multipurpose, diagnostic, and malware removal tool. It also has some curative ability.Modern malware will hide all, or most of itself from detection in a HijackThis log. HijackThis (HJT) is very popular, and if malware can hide from it, it has a better chance of survival. But mostly HJT fails to detect malware because, with the exception of some bug fixes and minor updates, it has not been updated in a long time. A brief history lesson… Merijn Bellekom is the creator and developer of HJT. He sold it to Trend Micro in March, 2007. Trend added an “Analyze This” button to collect data, updated HJT to be compatible with Windows Vista/7, and fixed a few bugs. While malware has evolved much since March 2007, HJT has not. The need for a more powerful diagnostic tool that is updated often spurred developers to create their own pseudo versions of HJT. Among them DDS by sUBs, RSIT by random/random, and of course OTL by OldTimer Of them, OTL is the most robust, and has the most advanced ability to remove malware. The most common use for OTL is to post a log in a malware removal forum for analysis by an expert. However, it’s also a good idea to run an OTL log as a baseline before running any advanced removal tools. In the event those tools don’t completely remove the malware, the OTL log can offer valuable information to remove the remainder. A complete and detailed OTL tutorial has just been made public. It has been available to experts and forum helpers for some time. While most people will never use all the features of OTL, or only use it to create a log, others will find all the information offered in the tutorial helpful. One of the most powerful features of OTL is its ability to run custom scans. This allows the log output to be modified very easily, and quickly adapt to the latest malware threats. An always up-to-date custom scan recommendation can be found in our Malware Cleaning Guide. Following is a “Quick Start” Guide to creating an OTL log:
- Simply Download OTL.exe (alternate mirror) to your desktop, download folder, or other convenient location. In the event malware is blocking OTL.exe from running, alternate versions are available as either .com (mirror), or .scr (mirror).
- OTL doesn’t need to be installed, simply run it by clicking the icon (approve any UAC warnings on WIndows Vista or 7).

- First paste custom scan information (if any). Second, click the “Quick Scan” button.
 4. When the scan completes, it will open two windows in Notepad. OTL.txt, and Extras.txt. They are saved in the same location as OTL.exe. Copy the contents and paste to a forum for help, or if you’re an advanced user and have read the tutorial, analyze the output.
4. When the scan completes, it will open two windows in Notepad. OTL.txt, and Extras.txt. They are saved in the same location as OTL.exe. Copy the contents and paste to a forum for help, or if you’re an advanced user and have read the tutorial, analyze the output.
Wednesday May 12, 2010
Turn on Remote Desktop in Windows 7 or Vista
Wednesday May 12, 2010
Wednesday May 12, 2010
Turn on Remote Desktop in Windows 7 or Vista
Remote Desktop is disabled by default in Windows 7 or Vista, but it’s easy enough to turn it back on. If you need to access your Vista PC from another box, it’s an essential thing to turn on.
Important note: Remote desktop is only included in the Professional, Business, or Ultimate versions of Windows. Home editions do not have remote desktop.
To get to the configuration page, you can either right-click the Computer icon and choose properties, or you can type in system into the start menu search box, and then find the entry for System.
 Now you’ll want to click the Remote Settings link on the left hand side:
Now you’ll want to click the Remote Settings link on the left hand side:
 Now you can finally turn it on:
Now you can finally turn it on:
 To connect from another Vista / Win7 PC on the same network, click the bottom radio button. If you need to connect from an XP/2k machine, click the “Allow connections from computers running any version of Remote Desktop” radio button.
Don’t worry about setting up firewall rules, Vista or Windows 7 does that for you automatically.
Note: This should work for both Windows 7 and Vista.
To connect from another Vista / Win7 PC on the same network, click the bottom radio button. If you need to connect from an XP/2k machine, click the “Allow connections from computers running any version of Remote Desktop” radio button.
Don’t worry about setting up firewall rules, Vista or Windows 7 does that for you automatically.
Note: This should work for both Windows 7 and Vista.

Wednesday May 12, 2010
Seven tips for desktop malware first responders
Wednesday May 12, 2010
Wednesday May 12, 2010
#1Understand the risks Obey the First Responder’s Hippocratic Oath: Do no harm. In other words, don’t make things worse. Assess whether the malware needs to be removed immediately, or a better approach is to shut down the machine and pursue remediation in a controlled environment. Consider what data is at risk of being compromised vs. the current need for the device. #2 Carry a Web-enabled smart phone Pay for that data plan. Get reasonably proficient with a favorite mobile browser. Store bookmarks. Most phones support flash cards where additional remediation software can be stored. #3 Carry a big (16GB USB) stick At a minimum, consider carrying a hefty USB drive containing favorite anti-malware utilities, if not a fully bootable OS with security tools on it, such as Slax. #4 Check for broader attack Determine whether the attack is an ordinary bit of malware visiting your unlucky laptop, or a feint: a sequence of attacks designed to exploit the usual remediation steps rather than succeed with the initial infection. #5 Disaster recovery walkthrough Even if you’re fortunate enough to avoid a data loss on this occasion, it’s still worth exploring the disaster recovery options that might be been taken. They may need updating. #6 Update bookmarks The sobering experience may turn up some useful online security Web content. Update your phone’s bookmarks. #7 AAR and documentation In the military, it’s called “After Action Review,” or AAR. After the malware has been removed and damage corrected, assess which tools were needed and make them more convenient to access. Document what happened. Ensure that your CEO doesn’t encounter the same nuisance just before she heads out to testify before a Congressional subcommittee.

Monday May 03, 2010
Facebook to Share Your Info for Money
Monday May 03, 2010
Monday May 03, 2010
Facebook is now sharing your personal profile information with third parties. For now, it's just a few web sites, like the music site Pandora, and the consumer review site, Yelp. Facebook is automatically sharing that information, without your consent. If you don't want to share, you have to opt out. University of Minnesota law professor and privacy expert Bill McGevern says it's an important line in the sand. And for Facebook, with 600 million users, the stakes are high. “Facebook is trying over and over to get this shared so Facebook becomes the center of the web,” said McGevern. Facebook want to make money by selling user information. Last week, Facebook announced new features designed to unlock more of the data accumulated about its users during its six-year history. The senators said the recent changes by Facebook fundamentally alter the relationship between users and the social networking site. Before the change, users had control over what information they wished to share publicly and what information they wanted to keep private. Among other things, Facebook is plugging into other websites so people can communicate their interests with friends, colleagues and acquaintances online. Facebook also changed its own website to create more pages where users' biographical information could be exposed to a wider audience. In a statement, Facebook said, "these new products and features are designed to enhance personalization and promote social activity. All of Facebook’s partner sites interact with a user’s consent." To opt out of Facebook’s new profile sharing is a multiple step process: STEP 1: Go to the “Privacy Settings.” Go to “Applications and Web Sites.” Then go to “Instant Personalization Pilot Program,” and hit edit settings. STEP 2: For all users there’s an automatic check in the box below, which allows Facebook to share your information with other web sites. You are automatically “opted in.” If you do not wish to share this information, uncheck the box. STEP 3: Even after you’ve done this, it is not clear whether you need to “opt out” at the sites where Facebook is intending to share your information, like Pandora and Yelp, and soon many more sites. So you will want to look at the upper left hand corner of those sites to see whether those sites are recognizing your Facebook account and activity. Here again, you need to opt out. But a word of caution, as Facebook concedes, your information may still be shared through your friends accounts, unless you block the application from these web sites. Facebook, apparently responding to Congressional pressure, has already made some changes to this “Instant Personalization Pilot Program,” so you may want to periodically check back in to adjust your settings.

Sunday Apr 25, 2010
Windows 7 Product Key Checker 1.0.1
Sunday Apr 25, 2010
Sunday Apr 25, 2010
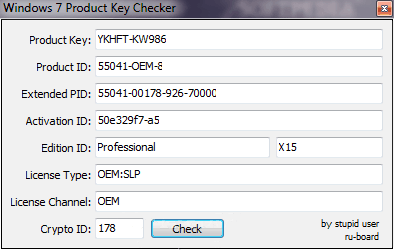
Here is a very useful utility Windows 7 Product Key Checker which lets you to check and verify your Windows 7 Product key. Windows 7 Product Key Checker is an easy to use application designed to offer you a full description of the every fields of the product key, Product ID, Extended PID, Activation ID, Edition ID, License Type, License Channel, and Crypto ID.
Windows 7 Product Key Checker 1.0.1
 Download Windows 7 Product Key Checker 1.0.1.
The PID is the product id assigned to each oem manufacturer by edition (ie Home Premium, Ultimate, etc.). You can find the PID for a product key by using the online PID checker: Windows PIDchecker.
Download Windows 7 Product Key Checker 1.0.1.
The PID is the product id assigned to each oem manufacturer by edition (ie Home Premium, Ultimate, etc.). You can find the PID for a product key by using the online PID checker: Windows PIDchecker.
Thursday Apr 15, 2010
New P2P Trojan Discovered
Thursday Apr 15, 2010
Thursday Apr 15, 2010
Once launched, the malware will install itself in the WINDOWS directory where it installs a registry key to ensure that it loads on startup.
Security researchers at Arbor Networks researchers have discovered a new botnet that compromises machines infected with the Heloag Trojan that is specifically designed to manage the downloading and installation of a spectrum of additional malicious software. “Upon detailed inspection, this bot does not appear to have any DDoS capabilities built into it, it appears to only manage downloads on the infected PC,” say researcher Jose Nazario. The way it works is that the trojan is downloaded from either 7zsm.com or elwm.net. Once on an infected PC, it then install itself in the WINDOWS directory. Names observed include:- C:\WINDOWS\csrse.exe
- C:\WINDOWS\ThunderUpdate.exe
- C:\WINDOWS\conme.exe
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon = [filename] (Where [filename] refers to the installed filename from above)It then makes a connection to the C&C server for the botnet, often on TCP port 8090, to register itself and await commands. Traffic is usually preceded by a single byte to indicate the message purpose:
- 01 – initial hello
- 02 – keep alive, idle message
- 03 – download the named file
- 04 – connect to other peers
- 05 – send hostname to server
- 06 – clear
- 07 – close connection

Sunday Mar 07, 2010
Ransom Malware Hits Internet
Sunday Mar 07, 2010
Sunday Mar 07, 2010
A Wave of Ransom Malware Hits Internet from : John E. Dunn, Techworld.com
 The attack itself takes the form of a spam e-mail with an attachment, report.zip, which if clicked automatically downloads a rogue antivirus product called Security Tool. It is also being distributed using manipulated search engine optimisation (SEO) on Google and other providers.
Such scams have been common on the Internet for more than a year, but this particular one features a more recently-evolved sting in the tail. The product doesn't just ask the infected user to buy a useless license in the mode of scareware, it locks applications and data on the PC, offering access only when a payment has been made through the single functioning application left, Internet Explorer.
What's new, then, is that old-style scareware has turned into a default ransom-oriented approach. The former assumes that users won't know they are being scammed, while the latter assumes they will but won't know what to do about it.
The technique is slowly becoming more common -- see the Vundo attack of a year ago -- but what is also different is the size of this attack, one of the largest ever seen by Fortinet for a single malware campaign.
Fortinet notes that Security Tool is really a reheat of an old campaign from November 2008, which pushed the notorious rogue antivirus product Total Security as a way of infecting users with a keylogging Trojan.
"This is a great example of how tried and true attack techniques/social engineering can be recycled into future attacks," says Fortinet's analysis.
According to Fortinet, the "engine" pushing the spike in ransom-based malware is believed to be the highly-resilient Cutwail/Pushdo botnet, the same spam and DDoS system behind a number of campaigns in the last three years including the recent pestering of PayPal and Twitter sites.
The attack itself takes the form of a spam e-mail with an attachment, report.zip, which if clicked automatically downloads a rogue antivirus product called Security Tool. It is also being distributed using manipulated search engine optimisation (SEO) on Google and other providers.
Such scams have been common on the Internet for more than a year, but this particular one features a more recently-evolved sting in the tail. The product doesn't just ask the infected user to buy a useless license in the mode of scareware, it locks applications and data on the PC, offering access only when a payment has been made through the single functioning application left, Internet Explorer.
What's new, then, is that old-style scareware has turned into a default ransom-oriented approach. The former assumes that users won't know they are being scammed, while the latter assumes they will but won't know what to do about it.
The technique is slowly becoming more common -- see the Vundo attack of a year ago -- but what is also different is the size of this attack, one of the largest ever seen by Fortinet for a single malware campaign.
Fortinet notes that Security Tool is really a reheat of an old campaign from November 2008, which pushed the notorious rogue antivirus product Total Security as a way of infecting users with a keylogging Trojan.
"This is a great example of how tried and true attack techniques/social engineering can be recycled into future attacks," says Fortinet's analysis.
According to Fortinet, the "engine" pushing the spike in ransom-based malware is believed to be the highly-resilient Cutwail/Pushdo botnet, the same spam and DDoS system behind a number of campaigns in the last three years including the recent pestering of PayPal and Twitter sites.
Thursday Feb 25, 2010
UNINSTALL Windows 7 Activation Update: KB971033 and REACTIVATE
Thursday Feb 25, 2010
Thursday Feb 25, 2010
For those of you who installed the Windows 7 Activation Checker update (KB971033) you can still uninstall it. The reason that viewers such as you may want to uninstall it, is because of the surround rumors that this update creates a new process/service that will slow down your system and has been rumored to monitor the user. If you haven’t installed this, you can go to Windows To Hide the Windows Update/Disable it From Ever Installing: 1. Go to Windows Update 2. Click to View Your Optional Updates 3. Right Click the one Labeled “Update for Windows 7″ with update ID “KB971033″ 4. Click “hide update.”
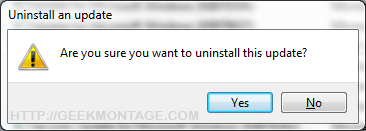
Uninstall KB971033 Windows 7 Activation Checker
takeown /f “%windir%\System32\Wat\*”5. Press enter 6. Type or right click -> paste:
icacls “%windir%\System32\Wat\*” /deny *S-1-1-07. Press enter and reboot. Reactivate Windows Method (easiest): If you need to re-activate your windows, it has been reported that Hazar’s and Daz’s activators work. Just type “Windows Activator Hazar Torrent” or “Windows Activator Daz Torrent” into Google. If you have changed your Windows Key and want to re-validate: 1. Go to start -> hold shift and click run (If you do not see run, simply type run in the start menu’s search box and click it while holding shift) Note: Holding shift while clicking run opens up run in administrative mode, which is necessary for this process. 2. Type in “command” or “cmd” and press enter. 3. Type the following or right click -> Paste:
%SystemRoot%\system32\Wat\WatAdminSvc.exe /run4. Hit enter and reboot. Remove Windows Activation Notification Mode 1. Go to start -> hold shift and click run (If you do not see run, simply type run in the start menu’s search box and click it while holding shift) Note: Holding shift while clicking run opens up run in administrative mode, which is necessary for this process. 2. Type in “command” or “cmd” and press enter. 3. Type the following or right click -> Paste:
takeown /F %WINDIR%\System32\sppcomapi.dll && icacls %WINDIR%\System32\sppcomapi.dll /deny *S-1-1-0:F4. Hit enter and reboot Note: You can re-enable this by typing:
icacls %WINDIR%\System32\sppcomapi.dll /grant *S-1-1-0:FRemove the WatU scheduled key checker: 1. Go to start -> hold shift and click run (If you do not see run, simply type run in the start menu’s search box and click it while holding shift) Note: Holding shift while clicking run opens up run in administrative mode, which is necessary for this process. 2. Type in “command” or “cmd” and press enter. 3. Copy and right click-> paste the following into command prompt:
schtasks /change /disable /tn “\Microsoft\Windows\Windows Activation Technologies\ValidationTask” && schtasks /change /disable /tn “\Microsoft\Windows\Windows Activation Technologies\ValidationTaskDeadline”Delete WAT Registry Entries Windows Activator logs all kinds of stuff about you… this is how to delete those logs. 1. Go to start -> hold shift and click run (If you do not see run, simply type run in the start menu’s search box and click it while holding shift) Note: Holding shift while clicking run opens up run in administrative mode, which is necessary for this process. 2. Type in “command” or “cmd” and press enter. 3.Right click -> paste the following into command prompt:
REG DELETE “HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Windows Activation Technologies” /f

Friday Feb 12, 2010
New Windows 7 update
Friday Feb 12, 2010
Friday Feb 12, 2010
The KB971033 update is scheduled to deploy to the manual downloading "Genuine Microsoft Software" site on February 16, and start pushing out automatically through the Windows Update environment on February 23.
 The update will reportedly be tagged simply as an "Important" update. This means that if you use the Windows Update system, the update will be installed to your Windows 7 PC based on whatever settings you currently have engaged for that level of update -- it will not otherwise ask for specific permission to proceed with installation.
An upcoming Windows 7 update (KB971033), due to be distributed to users in a few days time, will install an anti-piracy component that will contact a Microsoft server without your knowledge or permission every 90 days to check whether you are running a version of Windows tagged as pirated. For ever (or until you die and/or scrap your computer).
This nasty new tactic in the war against piracy is not good for a number of reasons. For one thing, the update has the power to start messing with your machine if it thinks you’re running a pirated copy of Windows 7 (never mind that your version has been fine up to that time), so it will turn your wallpaper black, and stick a nag screen up on your computer every so often and refuse to do any more updates.
Bear in mind that you don’t have to be guilty for this to happen, you just need to run afoul of the MS server database, so it *thinks* you’re in the wrong. And of course, who’s to say that eventually Microsoft won’t simply install a ‘Kill Switch’ to shut off those machines that it deems guilty of running pirate Windows?
And in case you’re thinking this is a great protection against piracy, just remember that professional pirates will immediately find a way around the update, just as they do every other such restriction, which means it’s the ‘ordinary joe’ user who’s going to suffer. That’s because the whole system is based around a database of pirated system signatures, e.g. serial numbers that have already been cracked and used for pirate copies.
The real problem with this is that at some point in the future your system signature may be ‘cloned’ by the pirates, or your hard disk may crash and the repairers install a compromised Windows 7 and bang, suddenly the database will think you’re a pirate, and your machine will be under the control of the dumb ox Microsoft machine. Good luck with getting rid of the downgrade of your system too.
Sigh, yet another example of a classic anti-customer action by the infamous Microsoft. I think I’ll just pop over to Control Panel and switch Windows Update to the manual approval setting for now. More detail can be found here at this Who Owns Your PC? post.
The new Microsoft WAT regime relies upon a series of autonomous “cradle to grave” authentication verification connections to a central and ever-expanding Microsoft piracy signature database, even in the absence of major hardware changes or other significant configuration alterations that might otherwise cause the OS or local applications to query the user for explicit permission to reauthenticate. Microsoft will trigger forced downgrading to non-genuine status if they believe a Windows 7 system is potentially pirated based on their “phone home” checks that will occur at (for now) 90 day intervals during the entire life of Windows 7 on a given PC, even months or years after purchase.
I recommend that you strongly consider rejecting the manual installation of the Windows Activation Technologies update KB971033, and do not permit Windows Update to install it (this will require that you not have your PC configured in update automatic installation mode, which has other ramifications -- so you may wish to consult a knowledgeable associate if you're not familiar with Windows Update configuration issues).
And if at some point in the future you find that the update has been installed and your PC is still running normally, remove the update as soon as possible.
The update will reportedly be tagged simply as an "Important" update. This means that if you use the Windows Update system, the update will be installed to your Windows 7 PC based on whatever settings you currently have engaged for that level of update -- it will not otherwise ask for specific permission to proceed with installation.
An upcoming Windows 7 update (KB971033), due to be distributed to users in a few days time, will install an anti-piracy component that will contact a Microsoft server without your knowledge or permission every 90 days to check whether you are running a version of Windows tagged as pirated. For ever (or until you die and/or scrap your computer).
This nasty new tactic in the war against piracy is not good for a number of reasons. For one thing, the update has the power to start messing with your machine if it thinks you’re running a pirated copy of Windows 7 (never mind that your version has been fine up to that time), so it will turn your wallpaper black, and stick a nag screen up on your computer every so often and refuse to do any more updates.
Bear in mind that you don’t have to be guilty for this to happen, you just need to run afoul of the MS server database, so it *thinks* you’re in the wrong. And of course, who’s to say that eventually Microsoft won’t simply install a ‘Kill Switch’ to shut off those machines that it deems guilty of running pirate Windows?
And in case you’re thinking this is a great protection against piracy, just remember that professional pirates will immediately find a way around the update, just as they do every other such restriction, which means it’s the ‘ordinary joe’ user who’s going to suffer. That’s because the whole system is based around a database of pirated system signatures, e.g. serial numbers that have already been cracked and used for pirate copies.
The real problem with this is that at some point in the future your system signature may be ‘cloned’ by the pirates, or your hard disk may crash and the repairers install a compromised Windows 7 and bang, suddenly the database will think you’re a pirate, and your machine will be under the control of the dumb ox Microsoft machine. Good luck with getting rid of the downgrade of your system too.
Sigh, yet another example of a classic anti-customer action by the infamous Microsoft. I think I’ll just pop over to Control Panel and switch Windows Update to the manual approval setting for now. More detail can be found here at this Who Owns Your PC? post.
The new Microsoft WAT regime relies upon a series of autonomous “cradle to grave” authentication verification connections to a central and ever-expanding Microsoft piracy signature database, even in the absence of major hardware changes or other significant configuration alterations that might otherwise cause the OS or local applications to query the user for explicit permission to reauthenticate. Microsoft will trigger forced downgrading to non-genuine status if they believe a Windows 7 system is potentially pirated based on their “phone home” checks that will occur at (for now) 90 day intervals during the entire life of Windows 7 on a given PC, even months or years after purchase.
I recommend that you strongly consider rejecting the manual installation of the Windows Activation Technologies update KB971033, and do not permit Windows Update to install it (this will require that you not have your PC configured in update automatic installation mode, which has other ramifications -- so you may wish to consult a knowledgeable associate if you're not familiar with Windows Update configuration issues).
And if at some point in the future you find that the update has been installed and your PC is still running normally, remove the update as soon as possible.

Sunday Feb 07, 2010
How to Backup 64 Bit System with Free System Backup Software?
Sunday Feb 07, 2010
Sunday Feb 07, 2010



